We’ve all answered a seemingly legitimate number only to be met with the mechanical voice of a pre-recorded robot. It’s hardly avoidable, considering there were an estimated 45.9 billion robocalls in the U.S. in 2020. And these calls aren’t just annoying; they cost businesses billions of dollars in lost time and productivity.
Luckily, the telecom industry has a solution. In December 2019, the Telephone Robocall Abuse Criminal Enforcement and Deterrence (TRACED) Act was signed into law. This bipartisan piece of legislation intends to prevent telemarketers and scammers from making illegal robocalls. Among other things, the Act requires the FCC to establish a call authentication framework and mitigation criteria to prevent end-users from receiving fraudulent calls.
So let’s talk about that framework, known as STIR/SHAKEN.
What is STIR/SHAKEN?
Unfortunately, STIR/SHAKEN has nothing to do with a 007-inspired cocktail. It is, however, a framework designed to reduce fraudulent robocalls and illegal spoofing. Think of it as a set of standards that run in the background during a call to guarantee the validity of the calling party. Let’s break it down.
STIR is short for Secure Telephone Identity Revisited. It’s both the name of a working group within the Internet Engineering Task Force (IETF) and the shorthand for a technology that adds cryptographic signatures to call signaling requests. In other words, it prevents a caller from providing a calling number to the receiving party that they’re not authorized to use.
SHAKEN stands for Signature-based Handling of Asserted information using ToKENs. (I know, it’s a stretch.) It’s a standard that defines how voice providers like us should implement the STIR technology to ensure that originating calling party numbers are not illegally spoofed.
Together, STIR/SHAKEN describes a set of technical standards and operating procedures for implementing call authentication for calls carried over an IP network. The framework will enable originating voice service providers to attest to the validity of an asserted caller ID. (Imagine the provider stamping the outbound calls with a certified signature that can’t be faked.) On the other end of the call, the terminating provider will use the security certificate to validate that the caller ID attestation hasn’t been compromised along the way.
It’s worth clarifying that STIR/SHAKEN technically doesn’t block fraudulent calls. It’s more like a tool that can indicate whether fraud may be occurring.
What is STIR/SHAKEN Attestation?
In accordance with STIR/SHAKEN, an originating voice provider will stamp each outbound call with an attestation level. Think of it like a friend vouching for you; the provider attests to their relationship with the caller and validates their right to use the number. There are three different levels of attestation: full, partial and gateway.
Full or “A” attestation means that the service provider knows the customer and can vouch for their right to use the phone number they’re calling from. Partial or “B” attestation means the service provider knows the customer, but not the source of the phone number itself. Gateway or “C” attestation means that the service provider has originated the call onto the network, but can’t authenticate the call source.
How Does STIR/SHAKEN Work?
The best way to understand the STIR/SHAKEN framework is to look at the process of a call step by step.
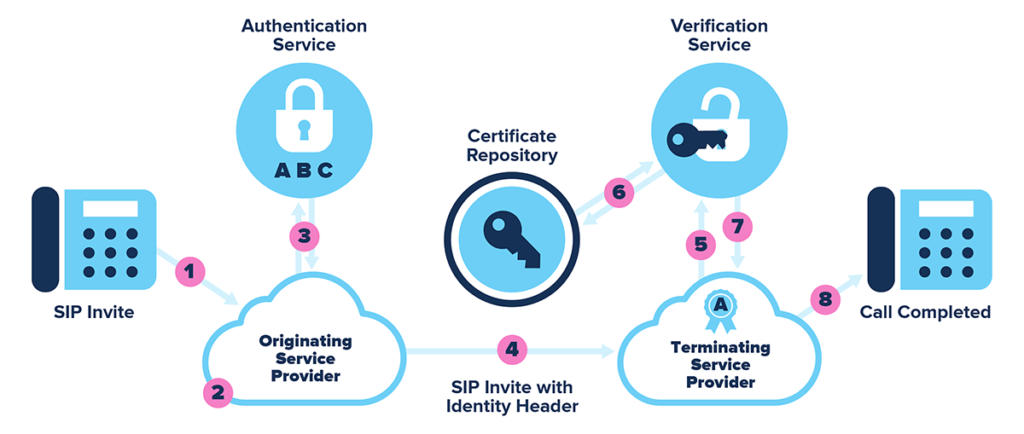
When a call is placed, a SIP invite is created by the caller (1). The caller’s service provider receives it (2) and checks the source and number of the call to determine the level of attestation (3).
Once the level of attestation has been determined, the provider creates an encrypted SIP identity header that includes the calling number, number being dialed, date and timestamp, level of attestation and a unique origination number for traceback (4). It’s as if each call receives it’s own ID.
At this point, the SIP identity header (and original SIP invite) are sent to the receiving provider (5), who passes the invite to a verification service (6). Once the information has been verified, the receiving provider can determine whether to block (7) or complete the call (8).
The Fight Against Fraud
Most Americans are hesitant about picking up the phone these days. According to Pew Research, only 19 percent of us will pick up a call from an unknown number. We’ve all been burned too many times by fraudulent calls telling us we’ve won a free night stay at the Marriott Hotel or an angry robobot telling us we’re about to be sued if we don’t take action NOW!
Today’s small businesses don’t have the luxury of not answering. When every call could be a potential customer, you can’t afford not to pick up.
The STIR/SHAKEN initiative is intended to make significant headway in the fight against fraud and to restore trust in our modern telecommunications.